I have been using this Crypto Exchange - changenow.io for at least a year now. I didn't realize they also had a bug bounty program which was mentioned in their footer section. I was quite busy with my day job so I kept the details of the program in my todo.txt so I could check it out later.
One night when I was having that itch of doing some bug bounties, I checked my todo.txt and decided to hunt bugs on changenow.io. I started by enumerating subdomains and probing for standard web ports (80/443). After obtaining a handful of URLs, I tried to visit them one by one and noticed a few of them were trying to redirect to another internal domain eth-btc.com
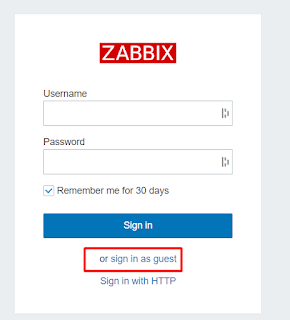
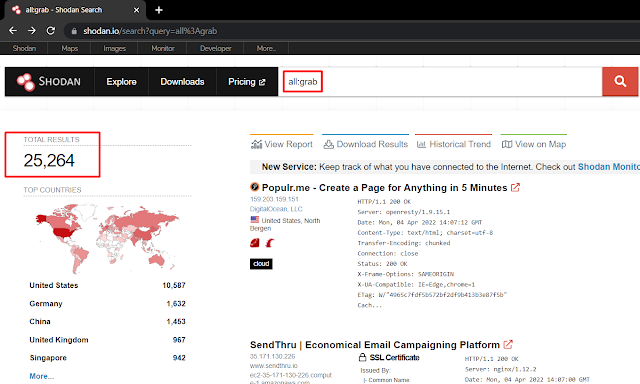
A quick whois on eth-btc.com revealed that it also belonged to changenow.io (admin email - sysadmin@changenow.io) so I enumerated the subdomains of this domain too. One of the subdomain zbx.sup.eth-btc.com was running Zabbix instance. I didn't have login credentials and common creds also didn't work but there was "Sign in as guest" option available.
From my prior CTF experience, I knew that this would still be helpful for me. So, I signed in as guest and I could see many interesting data of changenow.io.
There were some error logs in the monitoring dashboard which led me to the discovery of another internal domain - eth-btc.net. Again, the same process as above - enumerate subdomains and scan for web ports 80/443.
While checking the obtained URLs one by one, most of them were returning 403 errors but one of them named argo-ws.stage.aws.eks.eu.1.eth-btc.net returned some kind of dashboard without any authentication. It was Argo workflow dashboard.
I've seen similar types of dashboards related to DevOps many times before while doing recon, and they weren't always useful to me. However, I lazily typed this exact keyword "argo workflow hackerone" to find any publicly disclosed reports on HackerOne related to "Argo Workflow". It didn't yield any report from HackerOne but a medium blog popped up with RCE and Container Escape as root. Niceeee.
Again, I didn't have any hope that it would actually work and I'd get a shell but I created a workflow anyway by adjusting the poc.yaml such that I would receive a reverse shell to my external server if the exploit worked. Upon setting up netcat listener on my server and running the newly created malicious workflow, root shell was immediately obtained.

I was not able to execute commands directly so I used backticks (`) to get my commands executed and obtained a full TTY root shell.
After obtaining the TTY shell, I tried reading few files like /etc/hosts, /etc/passwd, list docker containers and viewed the contents of /root directory, and took screenshots for writing the report.
Impact
An attacker could view/modify any files of the server as root, read AWS keys, start/stop docker containers, plant rootkits/backdoors/keyloggers.. or just rm -rf / 💁♂️
Finding this issue was really fun. When starting with this program, I didn't have any goal of finding anything critical and just went with the flow and kept following the hints. It honestly didn't even felt like a real-life bug bounty finding but more like solving 20 pts HackTheBox machine. It took less than an hour from zero to root shell and the thrill was real. BUT the communication gap from the program side and their no bounty decision totally ruined the mood :/
I sent all details of this issue at 12AM on July 28 and everything got fixed over the night silently with no reply. Then few mails were exchanged, they even got scared and asked for "Step by step recon process for finding eth-btc.com" and a month later they came up with the audacity to reply like..
It is what it is.. :)
Update: After this blog got posted, they decided to have another look and suddenly found it impacts prod too and awarded $1000 - their max bounty. Refer to the timeline below.
Timeline
July 28, 2021, 12:23 AM: Issue found and full details sent
Jul 28, 2021, 8:00 AM: No reply, silent fix - Zabbix Guest signin Disabled, whois details modified, host with argo workflow taken down
Jul 28, 2021, 9:00 AM: Follow up in the ticket - Sir any updates? no reply and u fix? wen bounty?
Jul 28, 2021, 9:42 AM: Their response - Yeah we fixed it, more updates soon.
Aug 2, 2021: How did you find eth-btc.com? Explain your recon process step by step.
Aug 2, 2021: Full details sent.
Aug 2 - Aug 31, 2021: Any updates? Wen bounty?
Aug 31, 2021, 7:30 PM: Non-prod env, nothing serious. Hence, no bounty for you.
Aug 31, 2021, 10:00 PM: This blog published
Sep 1, 2021: On
twitter - Every security-related issue always receives our immediate attention, and this one is no different. That is why our team is taking another — closer — look at the peculiar issue in question as we speak.
Sept 2, 2021: We apologize that we initially did not rate its importance high enough. As it was the test environment we considered it as a minor issue. But the test environment configuration mimics the production environment, and any form of intervention in our system is regarded as an important issue. Therefore our team has re-considered the bug you provided, and we would like to thank you for attracting our attention to it by providing you with a reward. We will be happy to pay 1000$ in any cryptocurrency you want. 👀
I would like to thank my bhamiya
Debangshu Kundu for proof reading this writeup :)









Comments
Post a Comment